We are proud to announce our first security conference - RuhrSec. The conference takes place in Bochum at our university (28.-29.4.2016). It is a non-profit conference, i.e. all profit resulting from the sold tickets will go to Gänseblümchen NRW e.V. (thanks to our sponsors and to the great university conditions, we hope it will be much :) ). As this is our first conference, we carefully invited some top-class speakers (mainly our friends) to present their recent work. Given the program that we have now, I think we do not have to shame and we can keep up with the best conferences.
To give some overview, on the first day we will start with a talk about SSL/TLS and backwards compatibility issues by Prof. Schwenk. He will give a high-level overview on the newest protocol version (1.3), and what can go wrong if you run this version in parallel with its predecessors (TLS 1.0 - 1.2).
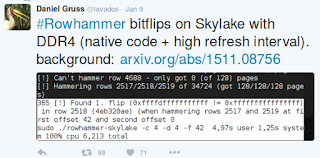
Next, Daniel Gruss will follow with a talk on Cache Side-Channel Attacks and the case of Rowhammer. Daniel's obsession is to flip bits in various memories, invoked from different environments. He is for example responsible for the RowhammerJS (Rowhammer invoked from Javascript). By following his tweets, it seems that he has a lot of interesting new stuff.
Let's see, what he will talk about at our conference.
Mario Heiderich, handsome heart-breaker and security researcher, will talk about his Relationship with AngularJS v2. The first version of this talk contained many AngularJS bypasses. We hope to see many more at our conference.
Johannes Dahse will present his tool for Detection of Complex Vulnerabilities in Web Applications. As the talk is complex, I do not even attempt to summarize this topic. It is however interesting to know that this work was awarded with the first Facebook Internet Defense Prize.
As there is no security conference without cats, RuhrSec will include two talks about these adorable animals. Martin Johns will talk about cats attacking WebRTC Communication. Marion Marschalek will talk about Alice's Adventures in Wonderland and about Cheshire Cat's Grin.
An IT buzzword coming more and more often at security conferences is IoT (I think this buzzword can currently be beaten only by SCADA). Therefore, Timo Kasper will present Security Nightmares in the Internet of Things: Electronic Locks and More. Do not worry that this will be only some boring "blah-blah" talk. Timo gives excellent research talks, he is known for example for his attacks on KeeLoq (technology used in garage doors):
You are still not impressed? There is more. At the end of the first day, just before a great dinner by G Data, Udo will give a workshop / InfoSec course on drinking wine, coffee and beer. I think this will be a highlight of the conference.
For further information, please see our program. This will include further talks by Felix 'FX' Lindner, Thorsten Holz, Marco Balduzzi, Mathias Bynens, Lucas Vincenzo Davi and Sebastian Schinzel.
To give some overview, on the first day we will start with a talk about SSL/TLS and backwards compatibility issues by Prof. Schwenk. He will give a high-level overview on the newest protocol version (1.3), and what can go wrong if you run this version in parallel with its predecessors (TLS 1.0 - 1.2).
Next, Daniel Gruss will follow with a talk on Cache Side-Channel Attacks and the case of Rowhammer. Daniel's obsession is to flip bits in various memories, invoked from different environments. He is for example responsible for the RowhammerJS (Rowhammer invoked from Javascript). By following his tweets, it seems that he has a lot of interesting new stuff.
Let's see, what he will talk about at our conference.
Mario Heiderich, handsome heart-breaker and security researcher, will talk about his Relationship with AngularJS v2. The first version of this talk contained many AngularJS bypasses. We hope to see many more at our conference.
Johannes Dahse will present his tool for Detection of Complex Vulnerabilities in Web Applications. As the talk is complex, I do not even attempt to summarize this topic. It is however interesting to know that this work was awarded with the first Facebook Internet Defense Prize.
As there is no security conference without cats, RuhrSec will include two talks about these adorable animals. Martin Johns will talk about cats attacking WebRTC Communication. Marion Marschalek will talk about Alice's Adventures in Wonderland and about Cheshire Cat's Grin.
An IT buzzword coming more and more often at security conferences is IoT (I think this buzzword can currently be beaten only by SCADA). Therefore, Timo Kasper will present Security Nightmares in the Internet of Things: Electronic Locks and More. Do not worry that this will be only some boring "blah-blah" talk. Timo gives excellent research talks, he is known for example for his attacks on KeeLoq (technology used in garage doors):
You are still not impressed? There is more. At the end of the first day, just before a great dinner by G Data, Udo will give a workshop / InfoSec course on drinking wine, coffee and beer. I think this will be a highlight of the conference.
For further information, please see our program. This will include further talks by Felix 'FX' Lindner, Thorsten Holz, Marco Balduzzi, Mathias Bynens, Lucas Vincenzo Davi and Sebastian Schinzel.